LabKey Server can be configured to automatically synchronize with an external LDAP server, so that any user and groups found on the LDAP server are duplicated on LabKey Server. This synchronization is one way: any changes made within LabKey will not be pushed back to the LDAP server.
Note that LDAP synchronization is independent of
LDAP authentication.
There are several options to control the synchronization behavior, including:
- Specifying a synchronization schedule
- Whether or not LabKey Server creates a user account corresponding to an LDAP user
- Whether or not LabKey Server creates groups corresponding to LDAP groups
- Deactivating a LabKey account for users with inactive LDAP accounts
- Synchronizing based on user and group filters
- Field mapping between the LDAP and LabKey user information
- Choosing to enforce or disallow the overwriting of user account information in LabKey
Syncing nested groups is not supported. Groups that are members of other groups must be manually configured in LabKey.
LabKey Configuration
To set up a LDAP synchronization connection:
- Edit the <LABKEY_HOME>/config/application.properties file to provide values for the following settings.
- Uncomment lines by removing the leading #.
- Replace "myldap.mydomain.com", "read_user" and "read_user_password" with the actual values appropriate to your organizations LDAP server.
#context.resources.ldap.ConfigFactory.type=org.labkey.premium.ldap.LdapConnectionConfigFactory
#context.resources.ldap.ConfigFactory.factory=org.labkey.premium.ldap.LdapConnectionConfigFactory
#context.resources.ldap.ConfigFactory.host=myldap.mydomain.com
#context.resources.ldap.ConfigFactory.port=389
#context.resources.ldap.ConfigFactory.principal=cn=read_user
#context.resources.ldap.ConfigFactory.credentials=read_user_password
#context.resources.ldap.ConfigFactory.useTls=false
#context.resources.ldap.ConfigFactory.useSsl=false
#context.resources.ldap.ConfigFactory.sslProtocol=SSLv3
Customers who wish to synchronize from multiple domains within Active Directory may want to investigate the
Global Catalog option, available via port 3268.
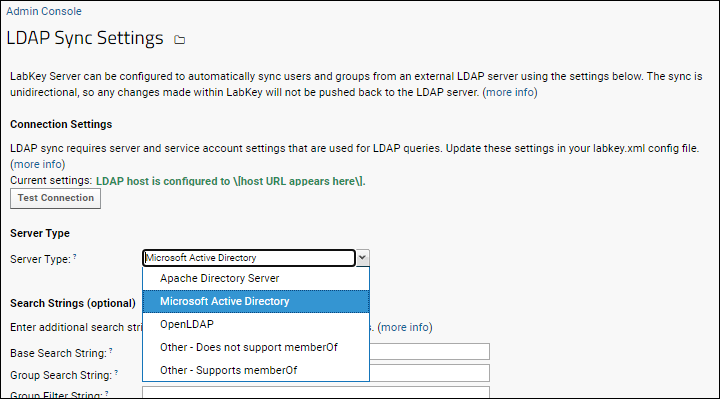
LDAP Sync Settings
Once the LDAP resource has been added, configure the synchronization behavior as follows:
- Go to > Site > Admin Console.
- Under Premium Features, click LDAP Sync Admin.
The page contains several sections of settings, detailed below.
Connection Settings
The
Current settings for your LDAP sync service and service account are validated in the background and if valid, will be displayed in green:
LDAP host is configured to [The host URL is shown here].
To test a connection with an LDAP server, click the
Test Connection button.
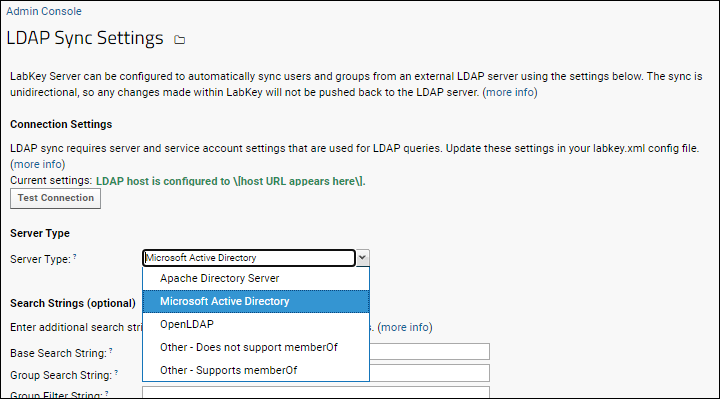
If the connection is not present or not configured properly, you'll see a red message instead, reading:
LDAP settings are not configured properly.
Server Type
The server type determines the approach taken for querying group memberships. Options include:
- Apache Directory Server
- Microsoft Active Directory
- OpenLDAP
- Other - Does not support memberOf
- Other - Supports memberOf
Search Strings
Use the
Search Strings section to control which groups and users are queried on the LDAP server. The appropriate values here are driven by the hierarchy and configuration of your LDAP server. Different LDAP server brands and versions have different requirements. In addition, each LDAP administrator is responsible for the structure and attributes of that organizations LDAP server. We strongly recommend consulting with your LDAP administrator to determine the appropriate search and filter strings for your purposes. We also recommend using an LDAP browsing tool to inspect the server's hierarchy and attributes; one option is the
Softerra LDAP Browser.
- Base Search String: The common root dn for all groups and users that should be synced. This dn is appended to the Group Search String and User Search String (see below) to establish the full dns from which to sync. If blank then the below Search Strings solely determine the dns for syncing. Example: dc=labkey,dc=com
- Group Search String: dn for syncing groups. This is relative to the Base Search String (or an absolute dn if Base Search String is blank). If blank then Base Search String determines the dn. Example: ou=Groups
- Group Filter String: A filter that limits the groups returned based on one or more attribute values. If blank then all groups under the specified dn will be returned. Example: (joinable=TRUE)
- User Search String: dn for syncing users. This is relative to the Base Search String (or an absolute dn if Base Search String is blank). If blank then Base Search String determines the dn. Example: ou=People
- User Filter String: A filter that limits the users returned based on one or more attribute values. If blank then all users under the specified dn will be returned. Example that returns all users with the "mail" attribute defined: (mail=*)
LDAP filters support multiple clauses and a variety of boolean operators. The syntax is documented on many LDAP tutorial websites. Here's one page (from the good folks at Atlassian) that provides a variety of examples:
How to write LDAP search filters.
You can also select a specific set of groups to synchronize using the graphical user interface
described below; any string settings made in the
Search Strings section override any groups chosen in the graphical user interface.
Field Mapping
Use
Field Mappings to control how LabKey Server fields are populated with user data. The labels on the left refer to LabKey Server fields in the core.Users table. The inputs on the right refer to fields in the LDAP server.
- Email
- Display Name
- First Name
- Last Name
- Phone Number
- UID
Sync Behavior
This section configures how LabKey Server responds to data retrieved from the synchronization.
- Read userAccountControl attribute to determine if active?: If Yes, then LabKey Server will activate/deactivate users depending on the userAccountControl attribute found in the LDAP server.
- When a User is Deleted from LDAP: LabKey Server can either deactivate the corresponding user, or delete the user.
- When a Group is Deleted from LDAP: LabKey Server can either delete the corresponding group, or take no action (the corresponding group remains on LabKey).
- Group Membership Sync Method: Changes in the LDAP server can either overwrite account changes made in LabKey, or account changes in LabKey can be respected by the sync.
- Keep in sync with LDAP changes
- Keep LabKey changes (this allows non-LDAP users to be added to groups within LabKey)
- Do nothing
- Set the LabKey user's information, based on LDAP? - If Yes, then overwrite any changes made in LabKey with the email, name, etc. as entered in LDAP.
- Page Size: When querying for users to sync, the request will be paged with a default page size of 500. If needed, you can set a different page size here.
Choose What to Sync
Choices made here are overwritten by any String Settings you make above.
- All Users (subject to filter strings above): Sync all users found on the LDAP system.
- All Users and Groups (subject to filter strings above): Sync all users and groups found on the LDAP system.
- Sync Only Specific Groups and Their Members: When you select this option, available LDAP groups will be listed on the left. To sync a specific group, copy the group to the right side. Click Reset Group List to clear the selected groups panel.
Schedule
- Is Enabled? If enabled, the schedule specified will run. If not enabled, you must sync manually using the Sync Now button below.
- Sync Frequency (Hours): Specify the cadence of sync refreshes in hours.
Save and Sync Options
- Save All Settings on Page: Click this button to confirm any changes to the sync behavior.
- Preview Sync: Provides a popup window showing the results of synchronization. This is a preview only and does not actually make changes on LabKey Server.
- Sync Now: Perform a manual, unscheduled sync.
Troubleshooting
If you have a large number of users and groups to be synced between the two servers, and notice that some user/group associations are not being synced, check to see if the page size is larger than the server's maximum page size. The default page size is 500 and
can be changed if necessary.
Related Topics
 If the connection is not present or not configured properly, you'll see a red message instead, reading:
If the connection is not present or not configured properly, you'll see a red message instead, reading: