This topic provides details about the options available for
configuration of password authentication in the database. Maintaining a strong security culture is a key component of data management, and requiring strong user passwords is one way to support that system.
Password Strength
By default, new instances of LabKey Server will use the "Strong" setting. Administrators can log in using a password that conforms to the strong rules and adjust the requirements if desired.
Good
"Good" password strength rules require that passwords meet the following criteria:
- Must be eight non-whitespace characters or more.
- Must contain three of the following:
- lowercase letter (a-z)
- uppercase letter (A-Z)
- digit (0-9)
- symbol (e.g., ! # $ % & / < = > ? @)
- Must not contain a sequence of three or more characters from the user's email address, display name, first name, or last name.
- Must not match any of the user's 10 previously used passwords.
Strong (Recommended)
"Strong" password strength requires that passwords meet a much stricter set of criteria. This level is recommended for all servers and is applied automatically to Sample Manager servers.
Passwords are evaluated using a modern scoring approach based on entropy, a measure of the password's inherent randomness. Long passwords that use multiple character types (upper case, lower case, digits, symbols) result in higher scores. Repeated characters, repeated sequences, trivial sequences, and personal information result in lower scores since they are easier to guess.
- This option requires 60 bits of entropy, which typically requires 11 or more characters without any easy-to-guess sequences.
- Must not match any of the user's 10 previously used passwords.
The user interface will provide a visual indicator of when the password you have selected meets the requirements. As long as the indicator bar is green and the text reads either "Strong" or "Very Strong", your password will be accepted.
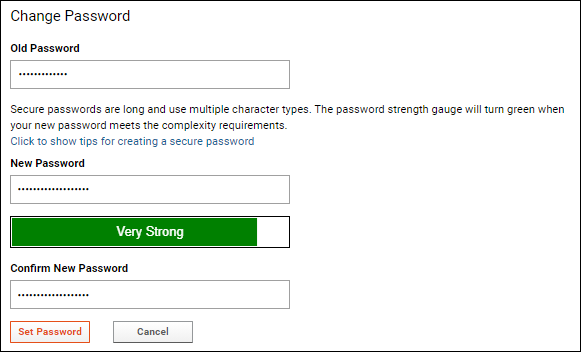
Additional detailed recommendations will be shown to the user if they
Click to show tips for creating a secure password.
Password Expiration
Administrators can also set the password expiration interval. Available expiration intervals are:
- Never
- Twelve months
- Six months
- Three months
- Every five seconds - for testing purposes
Password Best Practices for LDAP and SSO Users
For installations that run on LDAP or SSO authentication servers, it is recommended that at least one Site Administrator account be associated with LabKey's internal database authenticator as a failsafe. This will help prevent a situation where all users and administrators become locked out of the server should the external LDAP or SSO system fail or change unexpectedly. If there is a failure of the external authentication system, a Site Administrator can sign in using the failsafe database account and create new database authenticated passwords for the remaining administrators and users, until the external authentication system is restored.
To create a failsafe database-stored password:
- Select (User) > My Account.
- Choose Create Password. (This will create a failsafe password in the database.)
- Enter your password and click Set Password.
After setting up a failsafe password in the database, LabKey Server will continue to authenticate against the external LDAP or SSO system, but it will attempt to authenticate using database authentication if authentication using the external system fails.
Related Topics