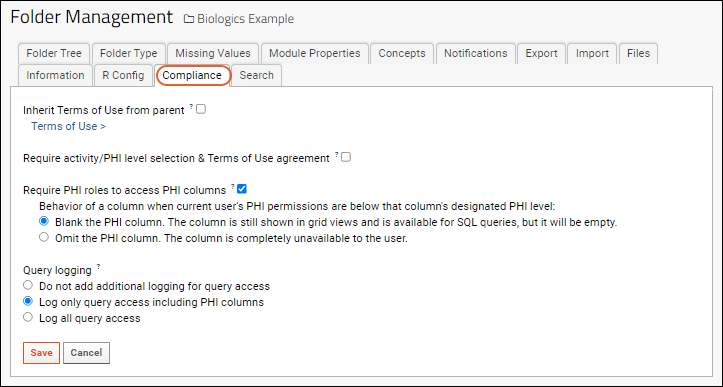
Compliance features offer several controls at the folder level:
Administrators can control the compliance features for a given folder by navigating to:
> Folder > Management. Click the
Compliance tab.
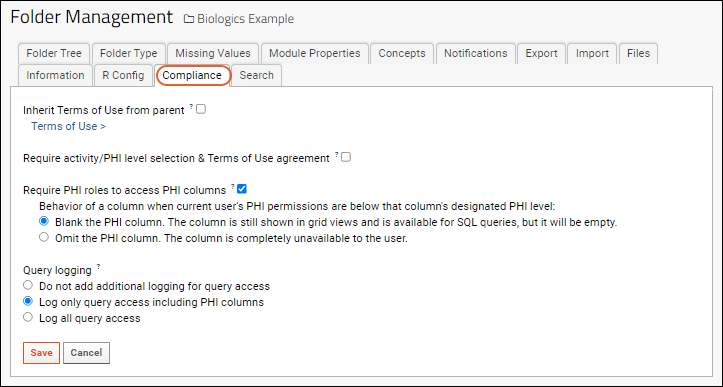
Terms of Use
To utilize any terms of use already present in the parent container (project or folder), check the box:
Inherit Terms of Use from parent.
Click
Terms of Use > to set new terms for this container
Require Activity/PHI Selection and Terms of Use Agreement
When enabled, users will be presented with a PHI level selection popup screen on login. The appropriate Terms of Use will be presented to them, depending on the PHI selection they make.
Require PHI Roles to Access PHI Columns
Role-based PHI handling prevents users from viewing and managing data higher than their current PHI level. Check the box to enable the
PHI related roles. When enabled, all users, including administrators, must be assigned a PHI role to access PHI columns.
You can also control the behavior of a column containing PHI when the user isn't permitted to see it. Options:
- Blank the PHI column: The column is still shown in grid views and is available for SQL queries, but will be shown empty.
- Omit the PHI column: The column will be completely unavailable to the user.
Note that if your data uses any
text choice fields, administrators and data structure editors will be able to see all values available within the field editor, making this a poor field choice for sensitive information.
Note that assay data does not support using PHI levels to restrict access to specific fields. Control of access to assay data should be accomplished by using folder permissions and only selectively copying non-PHI data to studies.
Query Logging
You can select three levels of additional logging, beyond
what is ordinarily logged by LabKey Server. Options:
- Do not add additional logging for query access
- Log only query access including PHI columns (Default)
- Log all query access
For logging details, see
Compliance: Logging.
Related Topics